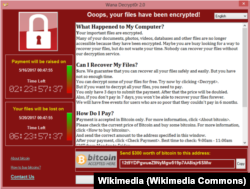
Last Friday, the largest cyberattack ever affected more than 200,000 computers in more than 150 countries. The attack used a virus that locked the computers' data. The attackers demanded payment to unlock the computers.
The virus, called WannaCry, infected computers in organizations including the British healthcare system, the American company FedEx and Russia’s Interior Ministry.
Our story, 'Ransomware' Affects Computers Worldwide explains more about the virus.
Although Friday's cyberattack was stopped, the virus may soon return in a different form. It is important to learn about the virus and the steps you should take now to protect your data from future versions of WannaCry.
How the virus locked computers
WannaCry attacked computers that were connected to the Internet and used Windows operating systems. The systems affected had not yet been updated with a security patch that Microsoft released in March.
How WannaCry was blocked
A developer accidentally discovered a way to prevent WannaCry from spreading. He looked at the computer code and noticed that the virus was directing computers to a domain name. He checked on the domain name and discovered that it was available, so he bought it for less than $11. That simple move enabled a "kill switch" that prevented WannaCry from spreading further.
Unfortunately, the kill switch does not unlock computers that were already infected by the virus.
The developer has chosen to remain nameless but uses the Twitter account @malwaretechblog. He wrote a blog post that explains in detail how he happened to discover the kill switch for WannaCry. The post is called How to Accidentally Stop a Global Cyber Attacks.
But we are not safe yet
This cyberattack used a security hole that still exists for computers running older versions of Windows. Computers running Windows 10 that have not yet installed the update are also at risk.
The virus may attack again. All the hackers have to do to launch a new cyberattack is to change the domain name in WannaCry, then release the updated virus.
How to protect your data against future cyberattacks
You can protect yourself against future cyberattacks. Make sure to download the latest Windows security patch to your computer. Microsoft, the maker of Windows, has now released security patches for older versions of Windows that give protection against WannaCry.
For help, visit Microsoft’s page called “How to Keep Your Windows Computer Up-to-date.”
Permit automatic Windows updates if you do not want to worry about keeping your computer updated.
Also, make sure that you save, or back up, your data. Do regular backups of your data, both locally with an external drive and in the Cloud. That way you can protect your data when another cyberattack takes place.
Be sure not to click on links or download attachments in emails unless you are sure that they are not "phishing" emails from hackers. Although the WannaCry virus attack did not happen this way, others have happened this way in the past.
I’m Caty Weaver.
Carolyn Nicander Mohr wrote this report for VOA Learning English. Catherine Kelly Weaver was the editor.
Had you heard about the cyberattack last week? Were you affected by WannaCry? Have you updated your computer and downloaded the latest version of Windows (or MacOS if you use an Apple computer)? Do you backup your data regularly?
Share your thoughts in the Comments Section below or on our Facebook page.
________________________________________________________________
Words in This Story
cyberattack - n. an attempt by hackers to damage or destroy a computer network or system
virus - n. a program that is designed to harm a computer by deleting data, ruining files, etc., and that can be spread secretly from one computer to another
security patch - n. a software or operating-system update that is intended to correct an issue that could lead to hacking or viral infection
domain name - n. the part of a network address that identifies one or more web addresses
automatic - adj. having controls that allow something to work or happen without being directly controlled by a person
phishing - n. the practice of sending fake emails that appear to be from actual companies in order to get individuals to share personal information, such as passwords and credit card numbers